Amass – Advanced OSINT for Attack Surface Mapping
Published by Hackura Labs | Powered by Hackura Consult
Overview
In modern cybersecurity operations, understanding a target’s attack surface is critical. Amass is a powerful open-source reconnaissance tool built for deep DNS enumeration and external asset discovery.
It is widely used by penetration testers, red teamers, and security researchers to perform Open Source Intelligence (OSINT) and uncover hidden infrastructure linked to a domain.
Why It Matters
Real-world attacks rarely target obvious assets—hidden and forgotten systems are often the weakest links.
Amass helps you:
- Discover hidden subdomains
- Identify exposed services
- Map external infrastructure
- Reduce blind spots in security assessments
This makes it essential for:
- Penetration testing
- Bug bounty hunting
- Threat intelligence operations
Key Features
- Passive and active enumeration modes
- Integration with multiple OSINT data sources
- Subdomain brute forcing capabilities
- Graph-based network mapping
- Scalable reconnaissance workflows
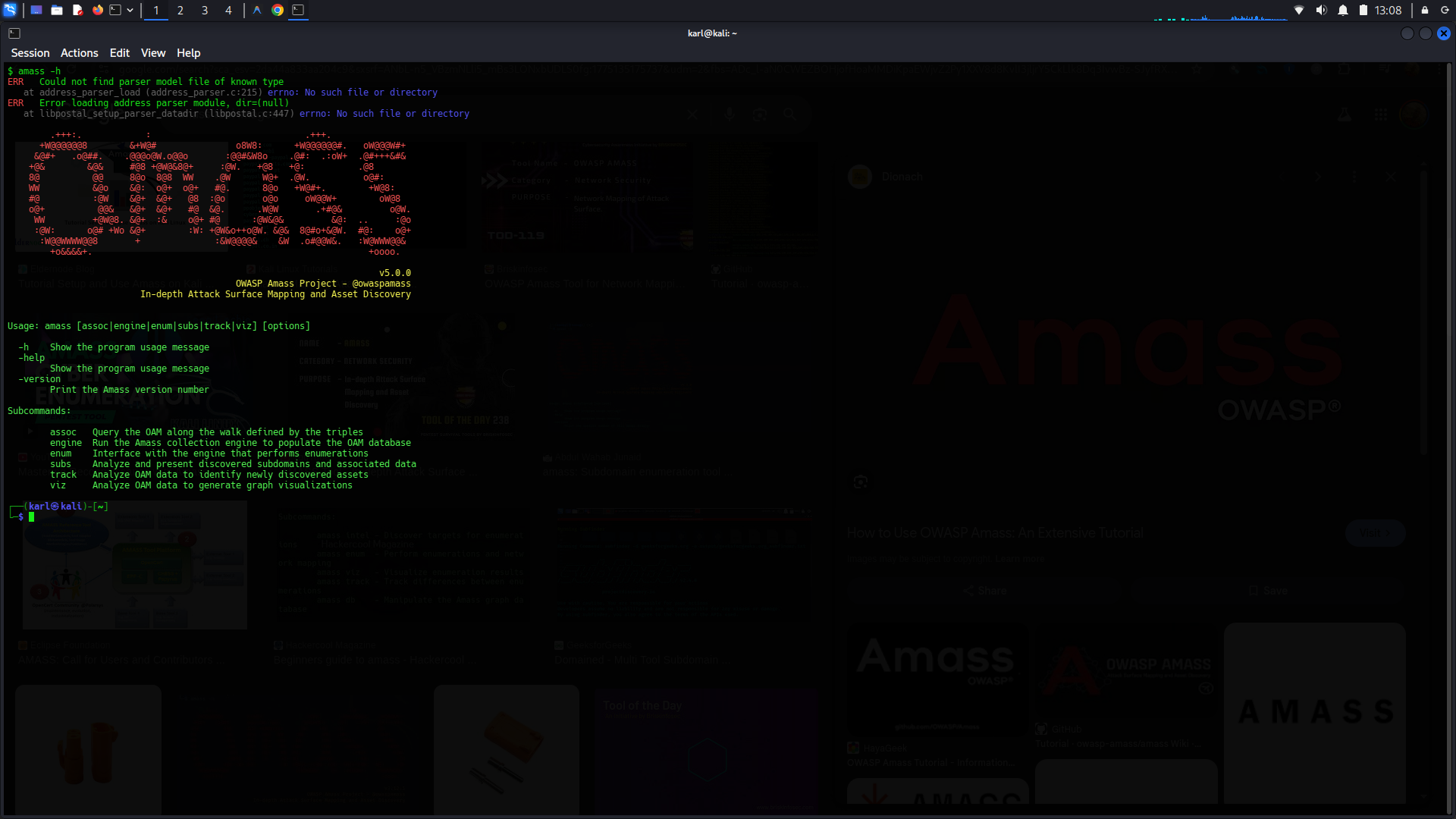
Basic Usage
Install (Kali Linux)
sudo apt install amass
Passive Enumeration
amass enum -passive -d example.com
Active Enumeration
amass enum -active -d example.com
Save Results
amass enum -d example.com -o results.txt
Real-World Use Case
Target provided:
mainwebsite.com
Amass may reveal:
- dev.mainwebsite.com
- api.mainwebsite.com
- staging.mainwebsite.com
These assets often expose:
- Misconfigurations
- Weak authentication mechanisms
- Unsecured APIs
Hidden assets frequently represent the highest-risk entry points.
Legal & Ethical Use
Use Amass only on:
- Systems you own
- Targets where you have explicit authorization
Unauthorized scanning is illegal and unethical.
Pro Workflow
For maximum effectiveness, integrate Amass into a recon pipeline:
- Nmap → Network and port scanning
- httpx → Live host detection
- Burp Suite → Vulnerability analysis
Official Resource
Final Thoughts
Amass is a cornerstone tool in modern reconnaissance. When used effectively, it provides deep visibility into external assets and significantly strengthens security assessments.


